Introduction
CyberSecurity threats are increasing across the globe. We take a look at how these threats have evolved on different mediums and over time. We grew up with computers before smartphones put the internet in everyone’s hand’s man, women, and children of modern society. Technology has improved drastically in decades. But with advanced technology and billions of mobile users there is huge data continuously getting generated and thus comes are question where does the data gets saved, how is the data used by respective service, internet provider, and most important ‘Is the Data Safe Online’?
Let Us Take a Look at Some of the Factors of CyberSecurity Threats
1. You’re Not Hacked but maybe Your Company is
Let’s take an example: you don’t have any social media accounts, and you have never shopped online. But you likely have an email address. You also have an employer and owe a bank account, and you do shop somewhere. All of these businesses do store your information. A hacker in such a case doesn’t even have to hack your computer or smartphone to get details. The hacker can go after hacking your email id and other company you do business with to get your data. And believe it or not, but this does happen all the time.
2. Your Governments may be Spying on You
Almost every government on all continents caught sometimes snooping on their citizens. No matter how safe you assume your personal data is, but it’s not safe from the government using for snooping. No matter wherever you are, there can be reasons some government agencies would be monitoring you.
3. Everyday CyberSecurity Threats
Losing your phone is equivalent to losing your wallet or keys. One may not realize how much personal information is available on the phone, it could be devastating in some cases. Well, in this case, there are measures that you can take to mitigate the risk by opting for a feature like ‘remote kill’. There are many free apps available on both android and ios that will not only able to locate the phone but will also make sure that the phone cannot retrieve, you can also remotely wipe the data from the phone.
4. Your Digital Life
What you post online will last even after you, but your social media account is part of a publicly owned company. Every game or app you install on your phone always wants your personal info and they do incentivize it by giving you some extra features, easier connectivity, and bonus items. Every time you use your social media accounts to log in to an app, you’re giving access to your personal information, and then they will sell and use this data as they see it to be fit. Have you ever notice there are many apps that don’t tell you that they’re not going to share your data, that’s because they will.
5. Hacking is Easier than You Think
The hard part of hacking isn’t about breaking into someone’s system. With a few attempts, a hacker can get into anyone’s network or computer. The hard part is about knowing what to look for and where. There are no good or bad people, only good or bad actions, and so thus the people hack for good and bad reasons.
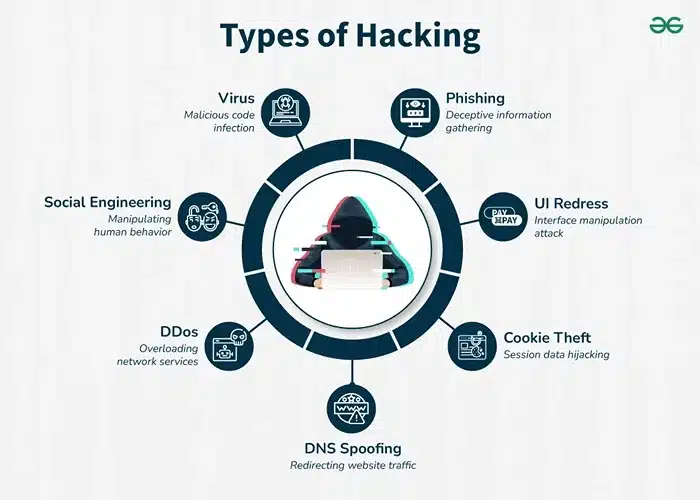
Source: geeks for geeks
6. You are being Stalked
You may think you’re not worth it, but the reality is everyone is worth watching. Whenever you apply for a job, there is a high chance that your potential employers will stalk you. When you meet someone new, they may stalk you. Your family, friends, exes, rivals, and others are probably stalking you. People may not admit it publicly, but we all are the culprits. Basic password protection guidelines and privacy settings can reduce this risk.
7. Social Hacking is an Easy
Even if you’re technically cautious, you may not realize how vulnerable your social presence is. Social hacking is the most common way of cyber-attacks and not technical programming. For example, ‘How a careless employee from an IT department of a company fooled by a link in an email appearing officially sent from his or her bank, or a manager or from the superior in the company. Or he herself/ himself by visiting an attractive website to reveal his/ her important authorization credentials, which were later passed on to the hackers’.
Conclusion
These pointers mentioned above are few but with the continuous evolution of technology and even the fringe elements are evolving not only this how the data collected from you is used in the further development of technology like Machine Learning (ML) or Artificial Intelligence (AI) has changed.
Although it’s almost impossible to get detached from the digital world and be an alien. It is important that we take steps advised by cybersecurity experts to be secure as much as possible. It’s also important for the companies who collect data to be accountable to protect and keep data safe online as we do at PromptCloud.