IP Bans Are Not the Problem
IP bans are not random blocks. They are the outcome of detection systems identifying non-human behavior patterns. You can reduce bans using proxies, user-agent rotation, and request throttling, but these are short-term fixes. At scale, websites evaluate multiple signals together, including fingerprinting and behavioral consistency. Reliable scraping requires a system-level approach. That includes adaptive request patterns, distributed infrastructure, compliance-aware data collection, and continuous monitoring of detection signals. If your scraper frequently gets blocked, the issue is not just your IP. It is how your entire scraping pipeline behaves.
Most teams treat IP bans as a surface-level issue. Rotate a few proxies, slow down requests, switch user-agents, and move on.
That works… until it doesn’t.
At a small scale, basic tactics can keep your scraper running. But as soon as you increase volume, target dynamic websites, or rely on data for business-critical decisions, IP bans stop being an occasional nuisance. They become a system failure signal.
Modern websites don’t just block IPs. They detect patterns across:
- Request behavior
- Browser fingerprints
- Session consistency
- Traffic anomalies
IP bans are just the final action. The real problem starts much earlier.
This is where most scraping setups break. Not because they lack proxies, but because they are not designed to operate in environments where detection systems are constantly adapting.
In this guide, we move beyond basic tactics. You’ll learn how IP bans actually work today, why most bypass strategies fail at scale, and how to design scraping systems that remain stable, compliant, and reliable over time.
Why IP Bans Happen in Modern Web Scraping
IP bans are not triggered by a single rule like “too many requests.” They are the result of multi-layered detection systems evaluating whether your traffic behaves like a real user or an automated system.
Most blogs oversimplify this into rate limits. That’s outdated.
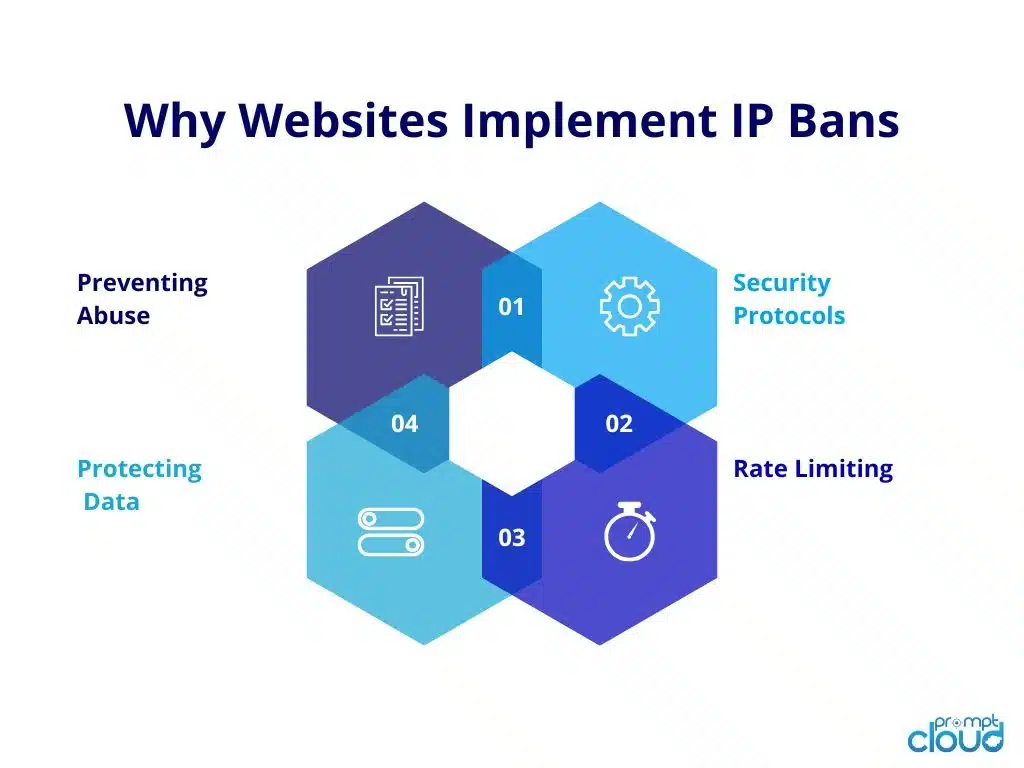
Today, websites use a combination of network-level signals, behavioral analysis, and fingerprinting techniques to identify scraping activity. IP blocking is just one enforcement mechanism after detection is confirmed.
According to industry benchmarks and security frameworks like OWASP automated threat models, bot traffic now accounts for a significant share of total web traffic, which has pushed websites to adopt far more sophisticated detection systems.
1. Rate Limiting Is the First Layer, Not the Only One
The simplest trigger is still requesting volume. If a single IP sends too many requests in a short time window, it gets flagged.
But modern systems go further. They track:
- Request bursts vs steady human-like intervals
- Repeated access to specific endpoints (like product pages or APIs)
- Concurrent sessions from the same IP
This means even “slow scraping” can get flagged if the pattern is predictable.
2. Behavioral Pattern Detection
Websites analyze how users navigate, not just how often they request data.
Human behavior has noise:
- Irregular click paths
- Time gaps between actions
- Scroll and interaction patterns
Scrapers, on the other hand, are often:
- Too linear (page → page → page)
- Too consistent (same delay, same sequence)
- Too efficient (no idle time, no randomness)
These patterns are easy to detect at scale.
3. Browser and Device Fingerprinting
Even if you rotate IPs, your scraper can still be identified through fingerprints.
Detection systems look at:
- User-agent consistency
- Screen resolution and device metadata
- Installed fonts, plugins, WebGL signatures
- TLS fingerprints
If multiple requests share the same fingerprint across different IPs, they can still be linked and blocked.
Stop getting blocked. Start receiving reliable web data
PromptCloud provides AI-ready data pipelines built on publicly accessible sources, with compliance<br>documentation, source provenance, and usage controls baked in.
• No contracts. • No credit card required. • No scraping infrastructure to maintain.
4. IP Reputation and Proxy Quality
Not all IPs are equal.
Datacenter proxies, especially overused ones, often carry a bad reputation. If your requests originate from known proxy networks, they are flagged faster.
Residential and mobile IPs perform better because they resemble real users, but even these can get blocked if usage patterns look automated.
5. Session and Cookie Inconsistencies
Real users maintain session continuity. Scrapers often don’t.
Red flags include:
- Missing or frequently reset cookies
- No session persistence
- Login flows that don’t behave like real users
Websites track this to detect automation.
Need This at Enterprise Scale?
While DIY scraping works for small-scale data collection or short-term projects, enterprise web data pipelines introduce constant site changes, anti-bot defenses, and reliability challenges. Most enterprise teams evaluate build vs buy to determine total cost of ownership.
What This Means for You
IP bans are not caused by a single mistake. They happen when multiple weak signals combine into a clear pattern.
This is why:
- Adding proxies alone doesn’t fix the problem
- Slowing down requests only delays detection
- Rotating user-agents without changing behavior still fails
To bypass IP bans reliably, you need to address how your scraper behaves as a system, not just how it sends requests.
How to Bypass IP Bans: What Actually Works (and Where It Breaks)
Most scraping guides list tactics like proxies, user-agent rotation, and delays as standalone solutions. In reality, these are control levers, not fixes. They only work when applied together and aligned with how detection systems evaluate traffic.
The goal is not to “hide your IP.” The goal is to look indistinguishable from real user traffic over time.
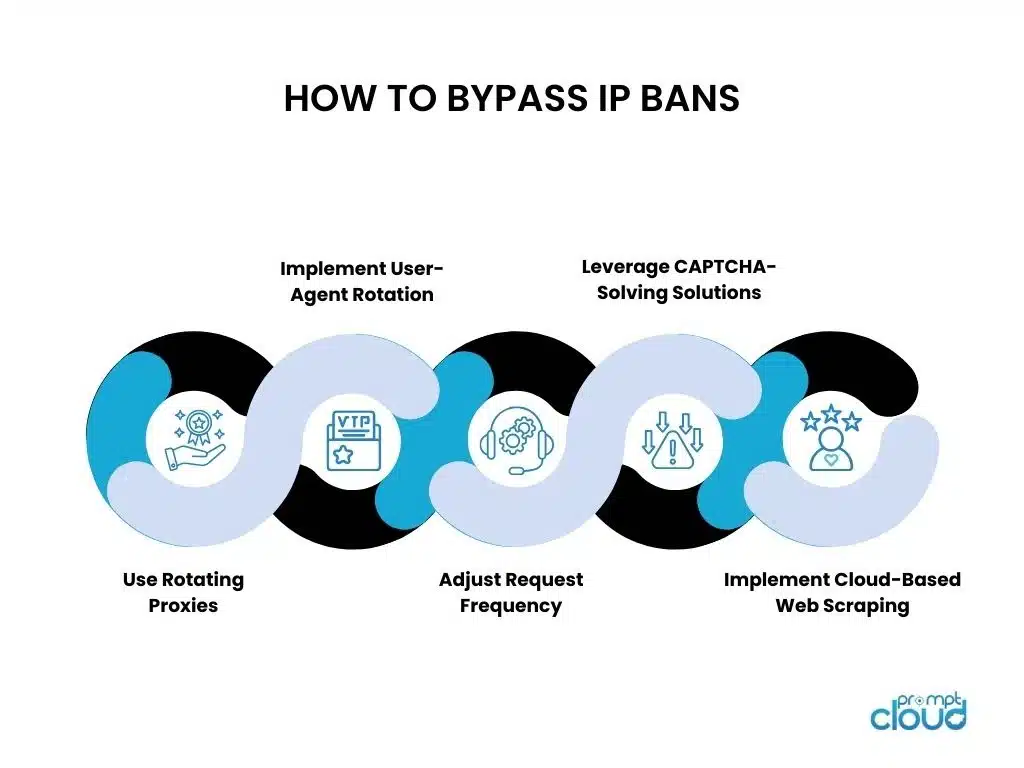
Proxy Rotation: Necessary, But Not Sufficient
Rotating IPs is the baseline. Without it, you will get blocked almost immediately on any high-value website.
However, proxies alone fail when:
- The same request patterns repeat across different IPs
- The fingerprint remains identical
- The traffic originates from low-quality or flagged proxy pools
High-quality residential or mobile proxies perform better because they inherit real-user characteristics. But even then, poor behavior will still get you blocked.
What works: Proxy rotation tied to request distribution logic, not just random switching.
Request Behavior: Where Most Scrapers Fail
This is the most ignored layer and the biggest reason scraping pipelines break.
Detection systems look for:
- Predictable intervals
- Sequential navigation
- High-efficiency data extraction patterns
If your scraper hits product pages in a clean loop with fixed delays, it will get flagged regardless of IP rotation.
What works: Introduce variability in:
- Request timing
- Navigation paths
- Session duration
This shifts your scraper from “script-like” to “behavior-like.”
Identity Layer: User-Agent Is Just the Surface
Rotating user-agents helps, but it’s only one part of a larger identity system.
Modern detection looks at:
- Header consistency
- Browser capabilities
- Device-level signals
If your scraper claims to be Chrome on Mac but behaves like a headless client, that mismatch becomes a detection signal.
What works: Consistent identity profiles across sessions, not random header changes per request.
Session Continuity: The Missing Piece
Real users don’t start fresh on every request. They carry forward:
- Cookies
- Session tokens
- Navigation context
Scrapers that ignore this appear unnatural.
What works: Maintain session persistence and simulate realistic browsing flows instead of isolated requests.
What This Means in Practice
Most “bypass strategies” fail because they are implemented independently.
The difference between a fragile scraper and a reliable one is this:
| Approach | Outcome |
| Proxies + delays + UA rotation (isolated) | Short-term success, frequent bans |
| Coordinated system (behavior + identity + infrastructure) | Stable, scalable scraping |
If your setup is still getting blocked, it’s not because you missed a tactic. It’s because the system is not coordinated.
Code Example: Handling IP Rotation and Request Control in Python
Most examples online show either proxy usage or request delays in isolation. That’s not enough. You need to combine IP rotation, headers, and request timing in a coordinated way.
Below is a simplified example that demonstrates how to structure requests more realistically.
import requests
import random
import time
# Sample proxy pool (replace with real provider)
proxies = [
“http://user:pass@proxy1:port”,
“http://user:pass@proxy2:port”,
“http://user:pass@proxy3:port”
]
# Sample user agents
user_agents = [
“Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 Chrome/120.0.0.0 Safari/537.36”,
“Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 Chrome/119.0.0.0 Safari/537.36”,
“Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 Chrome/118.0.0.0 Safari/537.36”
]
urls = [
“https://example.com/page1”,
“https://example.com/page2”,
“https://example.com/page3”
]
session = requests.Session()
for url in urls:
proxy = random.choice(proxies)
headers = {
“User-Agent”: random.choice(user_agents),
“Accept-Language”: random.choice([“en-US,en;q=0.9”, “en-GB,en;q=0.8”]),
“Referer”: “https://www.google.com/”
}
try:
response = session.get(
url,
headers=headers,
proxies={“http”: proxy, “https”: proxy},
timeout=10
)
print(f”Fetched {url} – Status: {response.status_code}”)
# Random delay to mimic human behavior
time.sleep(random.uniform(2, 6))
except Exception as e:
print(f”Error fetching {url}: {e}”)
What This Example Gets Right
This setup improves over basic scripts because it:
- Distributes requests across multiple IPs
- Introduces variability in headers
- Avoids fixed request intervals
- Maintains a session instead of stateless calls
Where This Still Breaks
Even this improved setup will fail when:
- Targets use advanced fingerprinting (browser-level signals)
- JavaScript-heavy pages require real browser execution
- Detection systems correlate behavior across sessions
- Proxy pool quality is low or overused
At that point, you move beyond simple scripts into:
- Headless browser orchestration
- Distributed scraping systems
- Managed infrastructure with adaptive controls
This is the inflection point where most DIY setups start becoming unreliable.
AI and Adaptive Scraping: How Modern Systems Handle Detection
Detection Systems Are No Longer Static
Web scraping used to be a game of rules. Stay under rate limits, rotate IPs, and avoid obvious patterns. That model no longer holds.
Today, websites rely on dynamic detection systems that continuously evaluate traffic behavior. These systems analyze how requests evolve over time, how sessions behave, and how closely traffic resembles real users. Blocking is no longer triggered by a single violation. It is the result of patterns accumulating across multiple signals.
This is why many scrapers fail without any visible change. The detection system has adapted, even if the website interface has not.
From Scripts to Feedback-Driven Systems
Traditional scrapers operate on predefined logic. They follow fixed request intervals, static navigation paths, and predictable extraction patterns. This makes them efficient, but also highly detectable.
Adaptive scraping systems work differently. They respond to signals from the target website. If response times increase, request rates adjust. If block patterns emerge, routing and behavior change. If page structures shift, extraction logic adapts.
The system is no longer executing instructions. It is continuously reacting to the environment it operates in.
Why This Shift Matters More in E-Commerce
E-commerce platforms are among the most actively defended environments. Pricing, availability, and product positioning are directly tied to revenue, which makes scraping activity a high-risk signal for these platforms.
As a result, detection systems are stricter, more responsive, and more sensitive to anomalies. A scraper that works reliably on static content sites will often fail quickly on e-commerce platforms because the expectations for “normal behavior” are much tighter.
This is where adaptive systems become necessary. They allow scraping pipelines to adjust in real time instead of breaking under changing conditions.
Traditional vs Adaptive Scraping Systems
| Dimension | Traditional Scraping | Adaptive / AI-Driven Scraping |
| Request behavior | Fixed intervals and patterns | Adjusts based on response signals |
| IP handling | Predefined rotation logic | Dynamic distribution based on risk |
| Detection handling | Retry after failure | Detects early signals and adapts |
| Site changes | Manual intervention required | Signals trigger automated adjustments |
| Scalability | Degrades as volume increases | Stabilizes through feedback loops |
What This Means Going Forward
The problem is no longer just avoiding IP bans. It is operating in an environment where detection systems are constantly learning and evolving.
A scraper that does not adapt will eventually become predictable. And once it becomes predictable, it becomes blockable.
Why DIY Scraping Breaks at Scale (and When to Move to Managed Services)
The Hidden Cost of “It Works for Now”
Most scraping projects start small. A few scripts, some proxy rotation, basic scheduling, and things seem stable. Data flows in, dashboards get updated, and the system appears reliable.
The problem shows up when scale increases.
More pages, more frequency, more targets, and suddenly the same setup starts failing. Requests get blocked more often. Data gaps appear. Maintenance cycles increase. Engineering time shifts from building features to fixing pipelines.
This is not an edge case. It is the default trajectory of DIY scraping systems.
Scale Introduces Compounding Failure Points
As scraping expands, multiple layers start breaking at the same time. Detection systems become more sensitive, proxy pools degrade faster, and site changes happen more frequently.
A single failure might seem manageable. But at scale, these issues stack.
Industry benchmarks suggest that over 40% of scraper failures in production environments are caused by site structure changes and anti-bot updates, not code logic itself. At the same time, teams report spending 30–50% of their scraping effort on maintenance rather than data extraction.
This shifts scraping from a data function into an operational burden.
Reliability Becomes the Real Problem
At scale, the question is no longer “can you scrape the data?” It becomes “can you trust the data pipeline?”
Unreliable scraping leads to:
- Missing or delayed data
- Inconsistent datasets across time
- Increased validation and reprocessing effort
For use cases like pricing intelligence, competitive monitoring, or inventory tracking, even small gaps can lead to incorrect decisions.
Why Teams Move to Managed Scraping Services
At this stage, teams start evaluating whether maintaining in-house scraping infrastructure makes sense.
Managed services solve a different problem. They are not just about extraction. They are about ensuring:
- Continuous data availability
- Adaptation to website changes
- Stability under scale and traffic variability
- Compliance with evolving data and privacy standards
Instead of reacting to failures, the system is designed to handle them proactively.
Where PromptCloud Fits In
PromptCloud is built around this exact shift from scraping as a script to scraping as a system.
Instead of managing proxies, handling blocks, and fixing broken pipelines internally, teams get structured, reliable datasets delivered through managed pipelines. The focus moves from “keeping scrapers running” to “using data to drive decisions.”
This is what separates experimental scraping setups from production-grade data infrastructure.
Legal and Compliance Considerations in Web Scraping
Scraping Is Not Illegal. But Unstructured Scraping Is Risky.
There is a persistent misconception that web scraping is inherently illegal. That’s not accurate.
Scraping publicly accessible data is generally permissible. The risk emerges from how the data is collected, what kind of data is being extracted, and whether the process respects platform policies and privacy regulations.
The shift over the last few years has been clear. Scraping is no longer just a technical problem. It is a compliance and governance problem.
Where Most Scraping Setups Go Wrong
Many scraping systems are designed with a single goal: extract data as efficiently as possible. Compliance is treated as an afterthought.
This creates exposure in areas like:
- Ignoring platform terms of use
- Collecting personally identifiable information without safeguards
- Failing to document data lineage and usage
- Lacking audit trails for enterprise environments
As data becomes more regulated, these gaps become liabilities.
Regulatory Pressure Is Increasing
Global data regulations have tightened significantly. Frameworks like GDPR and evolving data protection standards have made it essential to understand:
- What data is being collected
- Whether it includes sensitive or personal information
- How that data is stored, processed, and shared
Organizations are now expected to demonstrate not just data usage, but data responsibility.
Refer to the OWASP automated threat guidelines for a broader understanding of how automated systems are evaluated from a security and compliance perspective.
Governance Is Now a Core Requirement
Scraping pipelines need to be built with governance in mind from the start. This includes:
- Defining clear rules for data collection
- Masking or anonymizing sensitive fields
- Maintaining logs and audit trails
- Ensuring data usage aligns with intended purposes
This is where structured frameworks become critical. Teams that adopt approaches like ethical web data governance framework and privacy-safe scraping and PII masking approaches are able to scale without introducing compliance risks.
For enterprise teams, this often becomes part of a broader evaluation process using a web scraping vendor compliance checklist. In many cases, successful implementations are validated through internal or third-party audits, similar to this enterprise compliance audit success case study.
The Real Shift
The conversation has moved from:
“Can we scrape this data?”
to
“Can we justify how we collect and use this data?”
That shift defines how sustainable your scraping strategy will be.
Explore More
- Understand how to design scraping systems that protect sensitive data and reduce compliance risk using structured privacy-safe scraping and PII masking approaches.
- Before scaling scraping efforts, use this web scraping vendor compliance checklist to assess data governance, security practices, and operational reliability.
- Move beyond extraction and implement a structured ethical web data governance framework to ensure long-term sustainability and trust.
- See how organizations successfully pass audits using structured scraping practices in this enterprise compliance audit success case study.
Stop getting blocked. Start receiving reliable web data
PromptCloud provides AI-ready data pipelines built on publicly accessible sources, with compliance<br>documentation, source provenance, and usage controls baked in.
• No contracts. • No credit card required. • No scraping infrastructure to maintain.
FAQs
1. What is the best way to bypass IP bans in web scraping?
The most effective way to bypass IP bans is to combine proxy rotation, adaptive request timing, and consistent session behavior. Relying on a single tactic like proxies is not enough, as modern websites detect patterns across multiple signals, not just IP addresses.
2. How do you avoid getting banned while scraping websites?
Avoiding bans requires controlling request frequency, maintaining realistic browsing behavior, and using high-quality proxy infrastructure. Scrapers that mimic human interaction patterns and maintain session continuity are significantly less likely to be flagged.
3. Why do websites block web scraping attempts?
Websites block scraping to protect server resources, prevent data extraction by competitors, and maintain platform integrity. Modern systems also use detection models to identify automated traffic that deviates from normal user behavior.
4. Can web scraping work without proxies?
Web scraping without proxies is only viable for low-frequency or small-scale use cases. At scale, requests from a single IP quickly trigger rate limits and detection systems, making proxies or distributed infrastructure essential.
5. How do I know if my scraper is being blocked?
Common signs include sudden drops in data volume, repeated CAPTCHA challenges, inconsistent responses, or unexpected status codes. Soft blocks may return incomplete or misleading data, which makes monitoring critical.